
Table of Contents
Healthcare cyberattacks are tremendously growing. More and more patients, and large entities like hospitals, medical centers, and health insurance providers are continuously being affected. Whether it be patient data security, digital health safety, or medical data security, all fields are greatly impacted by hackers in healthcare. Even patient privacy data is not safe.
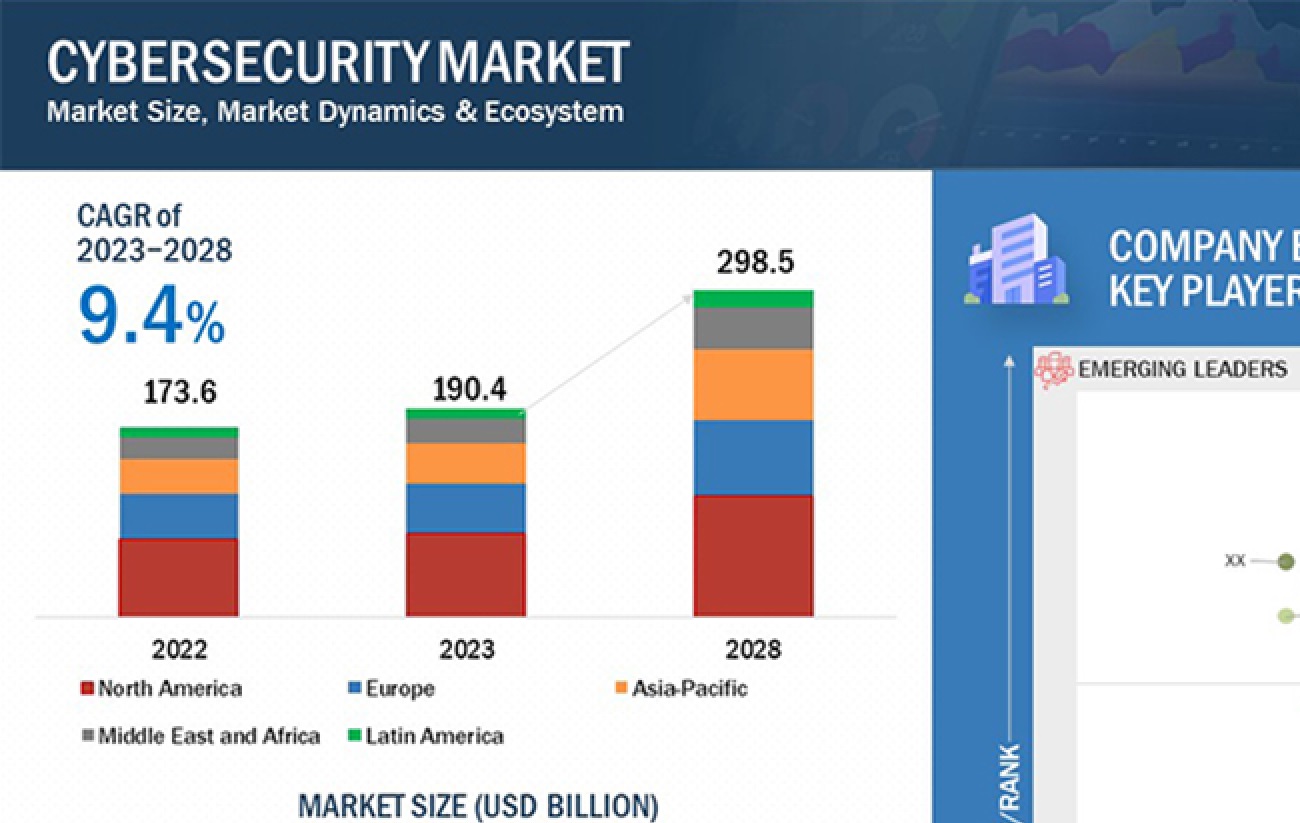
Healthcare cyberattacks are an alarming issue that calls for necessary measures to redress cyber threat mitigation. According to the Markets and Markets findings, the cyber risk management market is expected to reach $298.5 billion by 2028, registering a compound annual growth rate of 9.4% CAGR between 2023 and 2028.
As the need for proper healthcare IT security rises we thought of creating a quick guide that will clearly show you the current landscape of healthcare cyberattacks. This guide covers everything from top healthcare cyberattacks in the past 10 years, types of healthcare cyberattacks, and top cybersecurity policies to address this ongoing issue.
Top 5 Healthcare Cyberattacks in the Last 10 Years
Before you address the ongoing cyber resilience in healthcare, let us look into the top 5 healthcare cyberattacks that will show you how patient data security, digital health safety, and even medical data security are not safe.
1. Anthem Blue Cross Healthcare Cyberattacks
In January 2015, healthcare insurance provider Anthem Blue Cross was reported fallen prey to cyberattacks. During the cyberattacks, almost 78.8 million patients were affected as the hackers gained complete access to sensitive data such as credit/debit card pins, email addresses, and income information of the employees. This incident calls for the alignment of proper healthcare information systems in place.
2. Premera Blue Cross Healthcare Cyberattacks
Next on the list of healthcare cyberattacks comes another healthcare insurance provider named Premera Blue Cross. This cyberattack took place in 2015 where hackers stole both personal and financial information for over 11 million patients. This clearly shows that there is an urgent need for patient data security.
3. Excellus Blue Cross Blue Shield Healthcare Cyberattacks
Next on the list of popular cyberattacks comes the Excellus Blue Cross Blue Shield’s healthcare cyberattack. Excellus, being the largest healthcare insurance provider, suffered a data breach in September 2015 that caused more than 10 million patients to suffer. The breach involved stealing sensitive data such as social security numbers, telephone numbers, and some credit card numbers. This is also a big call for proper medical data security and actionable cybersecurity policies for the redressal of the problem at the earliest.
4. Banner Health Cyberattacks
Banner Health, a US-based non-profit healthcare insurance provider that is currently operating in 30 hospitals with several specialized medical facilities also suffered a cyberattack.
As reported by Banner Health, the healthcare providers faced threats relating to the patient’s privacy back to back in August 2016. During the threat, the hackers stole patient information and payment card records. Here as well the problem of digital health safety is mandatory now with proper cyber threat mitigation.
5. Accellion Healthcare Cyberattacks
The last but alarming call for cyber risk management is the Accellion healthcare cyberattacks. Accellion, a file transfer company, reported that its file transfer app (FTA) was hacked in December 2021. The company had legacy technology and many known security gaps that hackers were able to use and hack the data. As a result of this almost 100 companies were affected greatly.
Also, the most astounding report is that the hack began in the year 2021 and continued well up to 2022. Constantly being hacked for one year calls for proper digital healthcare information systems.
The report also claimed that hackers were able to access information for a host of companies including banks and healthcare providers. About this, almost 2.5 million patient records were hacked and there was a massive breach in the medical data security.
The above top five healthcare cyberattacks showcase that the integration of government and healthcare insurance providers is mandatory for the redressal of patient data security, digital health safety, and medical data security.
3 Common Ways of Healthcare Cyberattacks in 2024
Now that you are well aware of how crucial it is to address healthcare cyberattacks with proper cybersecurity policies. Let us look into the top five ways that hackers use to threaten the entire healthcare sector. This will help in executing a proper cyber threat mitigation policy.
1. Phishing
Phishing enters first on the list of healthcare cyberattacks. You must be aware that hospitals and clinics are fast-paced environments with constant urgency looming over their workers. These workplaces are often the perfect place for phishing since some employees are bound to not verify properly before sending over the information in the heat of the moment.
Email phishing is the most common type of phishing that is greatly influencing the healthcare sector. During email phishing, the hackers use advanced social engineering techniques and convince the victims to send all the sensitive information like patient data, credit cards, etc. This information is later sold or used to commit identity theft.
Cyber Threat Mitigation Tip for Phishing
One of the best cyber risk management tips for phishing is always to double-check the provenance of any email. It takes seconds to check the origin of an email, and spear-phishing attacks are usually relatively easy to detect since they’ll come from completely bogus addresses or similar ones but the wrong domain name.
2. Ransomware-as-a-Service
Ransomware-as-a-service falls second on the list of common ways of healthcare cyberattacks. For the past two years, cyberattacks such as data breaches or ransomware attacks have seen a rise in healthcare entities. In these cyberattacks, the hackers target the healthcare information systems of the largest healthcare insurance providers and start bypassing their security locks and encrypting all their sensitive information.
This not only causes loss of patient-specific sensitive data but also disrupts healthcare operations, affecting the lives of patients depending on it. As a result, digital health safety, and medical data security become quite crucial.
Cyber Threat Mitigation Tip for Ransomware-as-a-Service
One of the best cyber risk management tips for Ransomware-as-a-Service calls for running frequent backups of patient data and healthcare system reports. The backups of the information must be secured properly in an offline mode and a separate network segment. Look for regular monitoring and verify the integrity of restoring the systems in case of any cyberattacks.
3. Internet of Things (IoT) Vulnerabilities
Internet of Things (IoT) Vulnerabilities fall third on the list of common ways of healthcare cyberattacks. The healthcare industry has wholeheartedly adopted IoT devices to elevate patient monitoring, treatment, and healthcare delivery. Yet, the interconnectedness of these devices presents a formidable cybersecurity challenge. The reliance on IoT devices within healthcare amplifies the attack surface for cybercriminals, enabling them to exploit vulnerabilities, gain unauthorized access to sensitive information, or even disrupt critical medical equipment.
Cyber Threat Mitigation Tip for Internet of Things (IoT) Vulnerabilities
To reduce this type of healthcare cyberattack some of the best cyber risk management tips include – you can start conducting thorough security assessments of IoT devices before integration into the network. Ensure keeping track of IoT devices with an asset repository. You can also implement network segmentation to isolate IoT devices from critical healthcare systems. And, regularly update and patch firmware on IoT devices to address security vulnerabilities.
7 Steps To Prevent Healthcare Cyberattacks in 2024
Though healthcare cyberattacks are becoming a common issue, below we’ve highlighted seven cybersecurity policies that can protect healthcare businesses from cyberattacks.
1. Performing Risk Assessments
The first on the list of cybersecurity policies requires conducting risk assessments. To properly plan cyber resilience in healthcare first you need to assess the risk and level of risk involved.
Here every healthcare provider is required to review or assess the risk based on several factors such as how likely it is to happen and its impact on their organization. They also need to prioritize their risks. This means at least one risk assessment per year is required.
2. Implementing Basic and Advanced Security Controls
The second on the list of cybersecurity policies calls for the use of basic and advanced security controls. In other words, for proper cyber resilience in healthcare entities whether it be businesses, hospitals, insurance firms, or any healthcare service provider taking basic security control steps is necessary.
3. Staff Training and Education
The third on the list of cybersecurity policies for healthcare IT security calls for educating the staff. In this case, for proper cyber resilience in healthcare look into training doctors, nurses, assistants, secretaries, and all other staff who work at medical facilities, hospitals, and related entities.
4. Implementing Data Usage Controls
The fourth step on the list of implementing a proper healthcare information system requires having a data usage control module in place. Having a proper module in place will allow data providers to exercise control over the generated data by their sensors. This ensures that the policies put in place by the data producers are respected by data consumers.
5. Implementing Data Encryption
The fifth step on the list of implementing a proper healthcare information system requires using data encryption in place. This includes the files, patient data, and status, among other types of information, are all encrypted, and full patient data security and medical data security are achieved. For highly sensitive data, you can choose asymmetric encryption.
6. Securing Mobile Devices for Staff
The sixth step on the list of implementing a proper healthcare information system requires securing mobile devices for the staff. Similar to securing one’s devices at home, health insurance providers can also help their employees and other stakeholders secure their mobile devices, especially if they bring them to work.
7. Implement Off-site Data Backup
The last step on the list of cybersecurity policies for healthcare IT security calls for implementing off-site data backup. In other words, for proper cyber resilience in healthcare having the option of having a backup on a secure server elsewhere is the key.
By implementing the above seven steps, every healthcare entity can save themselves from the threats of healthcare cyberattacks.
Final Words
In essence, healthcare cyberattacks are highly a concerning issue. Whether you are running a hospital, clinic or serving as the largest healthcare insurance provider, addressing cyberattacks and taking measures for cyber resilience in healthcare is the key to safeguarding digital health safety. We hope with this blog the highly alarming issue is addressed at the earliest and necessary cybersecurity policies are taken against it.
Looking for a reliable platform that can provide medical updates in the healthcare sector? Discover the latest payers’ news updates with a single click. Follow DistilINFO HealthPlan and stay ahead with the timely payer’s news updates. Join our community today!
FAQs
1. What are the popular keys to cybersecurity policies for ensuring healthcare IT security and cyber resilience in healthcare?
Ans. Key cybersecurity policies for healthcare IT security and cyber resilience include performing regular risk assessments, looking for both basic and advanced security controls, and educating staff on cybersecurity best practices.
2. Why is patient data security and medical data security not safe in the context of healthcare cyberattacks?
Ans. Patient data security and medical data security are critical because healthcare cyberattacks lead to the theft of patient personal information like social security numbers, telephone numbers, and some credit card numbers. Safeguarding patient privacy requires taking necessary measures in the healthcare sector.
3. What are some common ways healthcare organizations can use to safeguard the healthcare information system and prevent cyberattacks?
Ans. Healthcare organizations can enhance their healthcare information system by implementing data encryption, securing mobile devices, and performing regular risk assessments.


